
Hiring a new employee is exciting. Whether it is your first hire or you are growing your team, onboarding usually focuses on the obvious things.
You need to:
But there is another part of onboarding that small businesses often overlook.
New employees may not know your security expectations yet.
This is especially true for:
For example, a new employee may not realize they should:
These things may seem obvious to someone who has worked in banking, tech, or a regulated industry.
They are not always obvious to someone early in their career.
That is why onboarding matters.
Good onboarding is not just about paperwork. It is about setting expectations clearly from day one.
Small businesses are busy. It is easy to focus only on getting employees working as quickly as possible.
The problem is that unclear expectations create unnecessary risk.
A simple onboarding process helps protect:
It also creates consistency as your company grows.
Many startups and small businesses struggle with balancing growth and security processes early on. That challenge becomes more noticeable as companies hire more employees, adopt more software, and begin working with larger customers.
Related: Top 5 Compliance Challenges for Tech Startups and How to Overcome Them
The good news is that this does not need to be complicated.
Even a simple checklist and a few clear policies can make a major difference.
Before a new employee starts, make sure you:
This is a simple starting point. It does not need to be perfect. It just needs to be consistent.
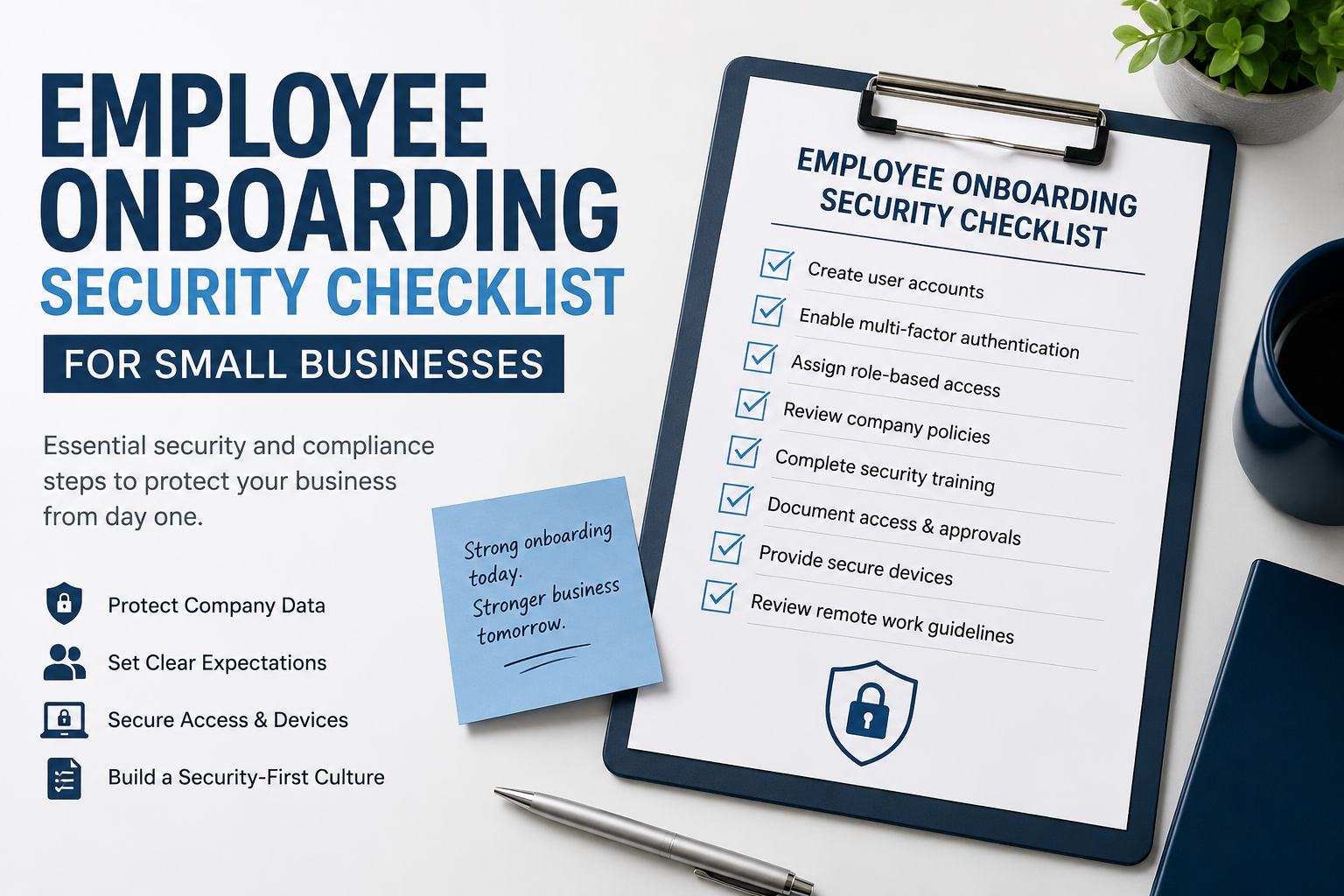
The quick checklist above is a good starting point.
For a more complete version, download the full New Employee Security and Compliance Checklist for Small Businesses.
It includes:
Every business should have employees review key policies during onboarding.
At minimum, consider:
These documents do not need to be overly formal or complicated.
The goal is simply to make expectations clear.
Many employees are never explicitly taught what is acceptable in a professional environment. Policies help create that shared understanding.
As businesses grow, having a clear process for policy management becomes increasingly important for consistency and governance.
Related: Why Policy Management Matters for SOC 2 and Good Governance
If your business uses:
then MFA should be enabled immediately.
Passwords alone are no longer enough to protect business systems.
For small businesses, MFA is one of the easiest and highest-impact cybersecurity improvements you can make.
One common mistake is giving employees access to everything because it is faster.
A better approach is to give employees only the access they need to do their job.
For example:
This is often called role-based access.
The concept is simple:
access should match the job.
Reviewing privileged access becomes increasingly important as companies grow and add more systems and employees.
Related: Why Privileged Access Reviews Matter and How They Help You Get SOC 2 Ready
Small businesses often grant access informally.
Someone sends a message, an account gets created, and everyone moves on.
The problem comes later when nobody remembers:
You do not need expensive software to fix this.
A simple spreadsheet or onboarding checklist can track:
This becomes very useful when:
Documenting employee access also makes offboarding much easier because you already know what systems the employee had access to.
Do not assume new employees already know cybersecurity basics.
A short onboarding discussion should cover:
This does not need to be a long training course.
Even a 15 to 30 minute discussion during onboarding is far better than assuming employees already know what to do.
The goal is to create awareness early and establish clear expectations.
Good onboarding and good offboarding work together.
When an employee leaves, your business should have a process to:
Former employee accounts are a common security risk for growing businesses.
Having a documented onboarding process also makes offboarding much easier because you already know what access the employee had.
Many employees do not know your expectations unless you explain them clearly.
Access should be based on role, not convenience.
Individual accounts improve accountability and make access easier to manage.
Security awareness should start during onboarding, not months later.
If access is not documented when granted, it becomes harder to review or remove later.
You do not need an enterprise-sized compliance program to improve employee onboarding security.
Start with the basics:
These simple steps help protect your business, your customers, and your employees.
They also help create stronger habits as your company grows.
Many of these same practices also support future SOC 2 readiness as businesses mature.
Related: SOC 2 Preparation Security Basics
Most importantly, good onboarding helps new employees succeed because expectations are clear from the beginning.
New employees should receive basic cybersecurity awareness training covering phishing emails, password security, MFA, handling customer data securely, and reporting suspicious activity.
Yes. Multi-factor authentication should be enabled for email, payroll systems, cloud platforms, password managers, and other business systems to reduce the risk of compromised accounts.
Most businesses should have employees review a Code of Conduct, Acceptable Use Policy, Confidentiality Agreement, Remote Work Policy, and password security expectations.
Documenting employee access helps businesses track who has access to systems, who approved the access, and when access was granted or removed. This becomes especially useful during offboarding, customer security reviews, and SOC 2 preparation.







