Many organizations only learn they need SOC 2 when a customer deal or vendor review is already in motion. J-SAS can help you document progress, explain your roadmap, and keep the conversation moving.
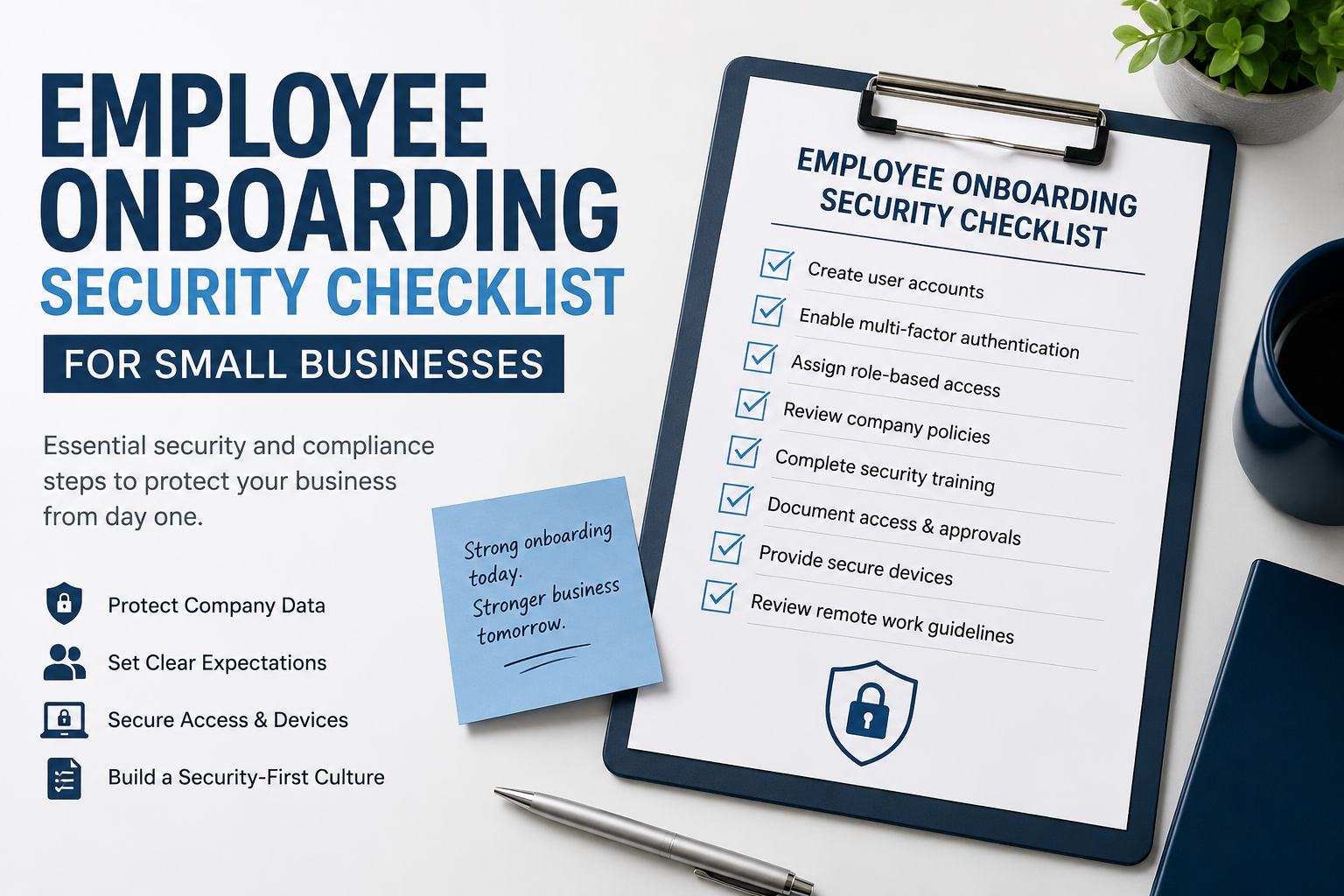
For teams with up to 20 employees, J-SAS offers simplified cybersecurity and compliance bundles to help you understand requirements, reduce risk, and prepare for reviews.